OPSWAT SBOM
Stay secure and compliant in the software supply chain. With OPSWAT SBOM (Software Bill of Materials), developers can identify known vulnerabilities, validate licenses, and generate component inventory for OSS (open-source software), third-party dependencies, and containers.
- Transparence de Supply Chain
- SBOM in CycloneDX & SPDX
- Vulnerability Insights
OPSWAT bénéficie de la confiance de
Automated
SBOM Creation
CycloneDX & SPDX Formats
7M+
Third-Party Open-Source
Software Components
CI/CD Pipeline
Integration
License Information
Vulnerability Awareness
Hidden Dependencies Put Your Software at Risk
Lack of Software Component Visibility
Development teams rely on open-source repositories and third-party components. Without a centralized SBOM, organizations cannot see what software is embedded in applications or containers.
Conformité et exigences réglementaires
Regulations like EU CRA, NIS2 Directive, EO 14028 and NIST frameworks require organizations to disclose software composition and risk. Manual SBOM creation is slow, inconsistent, and difficult to maintain across fast-moving development pipelines.
Unknown and Unpatched Vulnerabilities
When new CVEs emerge, teams without automated SBOMs can’t quickly identify affected dependencies. This delays incident response, extends exposure windows, and increases breach risk across the software supply chain.
Analyser, détecter, générer
Le moteur « Pays d'origine » analyse les empreintes numériques et les métadonnées des fichiers afin de déterminer leur provenance géographique et de déclencher des actions basées sur des règles.
You Develop Solutions. We Manage Risks.
Identify & Track Open-
Source Software
Automatically identify open-source components and monitor critical software updates and vulnerability patches from 5 million libraries.
Standardized SBOM
Structure for Tool
Interoperability
Support SBOM standardization with SPDX and CycloneDX formats for easier generation, sharing, and consumption.
Detect Vulnerabilities in
Software & Containers
Identify and reduce risk exposure across source code and containers by cross-referencing software components against trusted vulnerability databases like GHSA, CVE, and EUVD.
Stop Threats Infiltrating
Your Software Supply
Chain
Combine with Metascan™ Multiscanning and Proactive DLP™ to proactively detect over 99% of known malware and prevent secret exploits.
Flexible, Automated
Scanning
Constantly assess regulatory and internal security guidelines through real-time reports tailored for security engineers and GRC (Governance, Risk, and Compliance) teams.
Avoid Non-
Compliant Licenses
Validate and use approved licenses for OSS and third-party dependencies. Identify high-risk licenses like GPL, AGPL, MIT, and more.
Une solution unifiée pour sécuriser les Software
Scan your code and containers, identifying dependencies and vulnerabilities in open-source dependencies all at once from
a unified developer security platform.
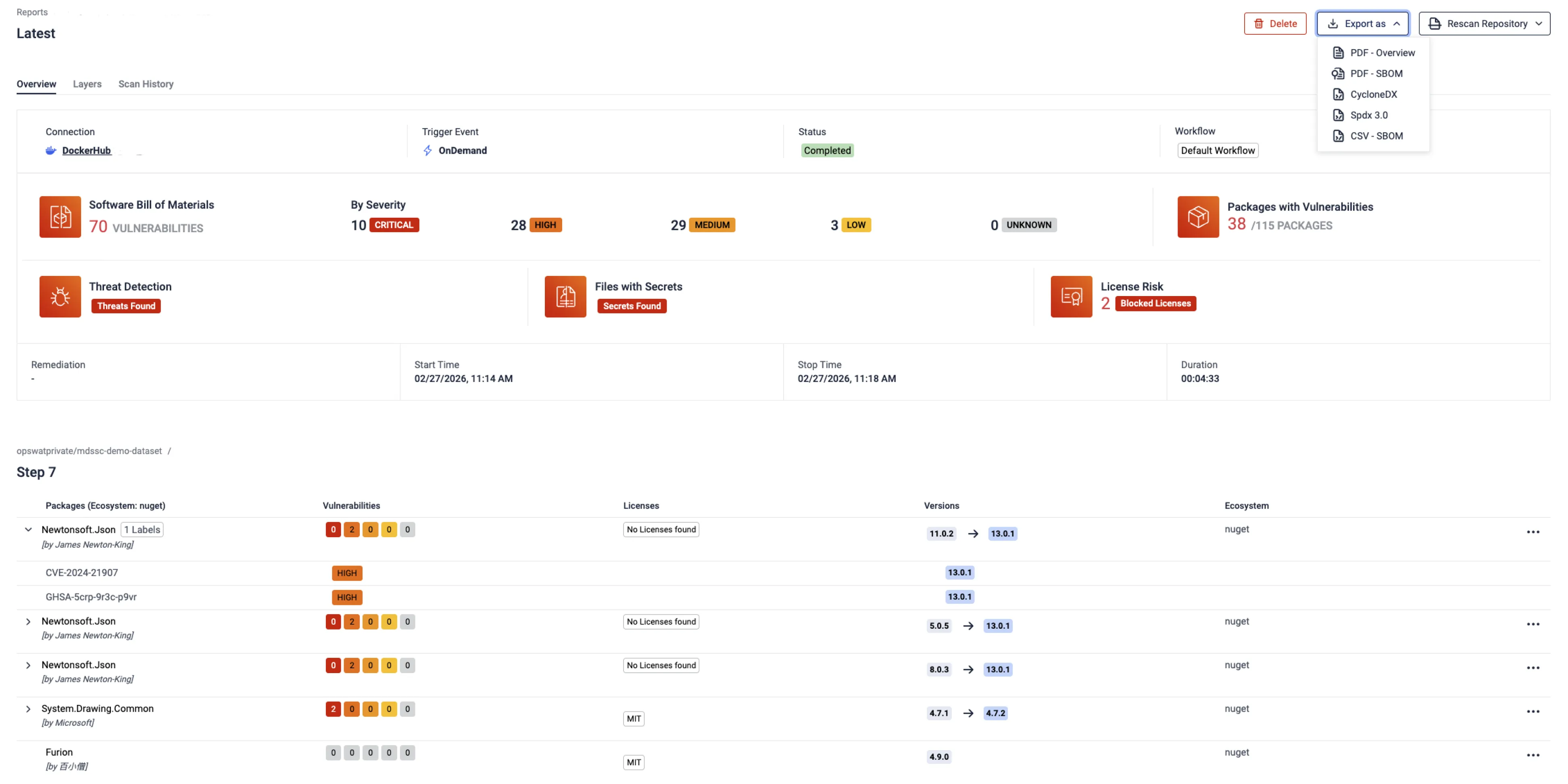
Provides visibility into all software components and vulnerabilities identified during the scan.
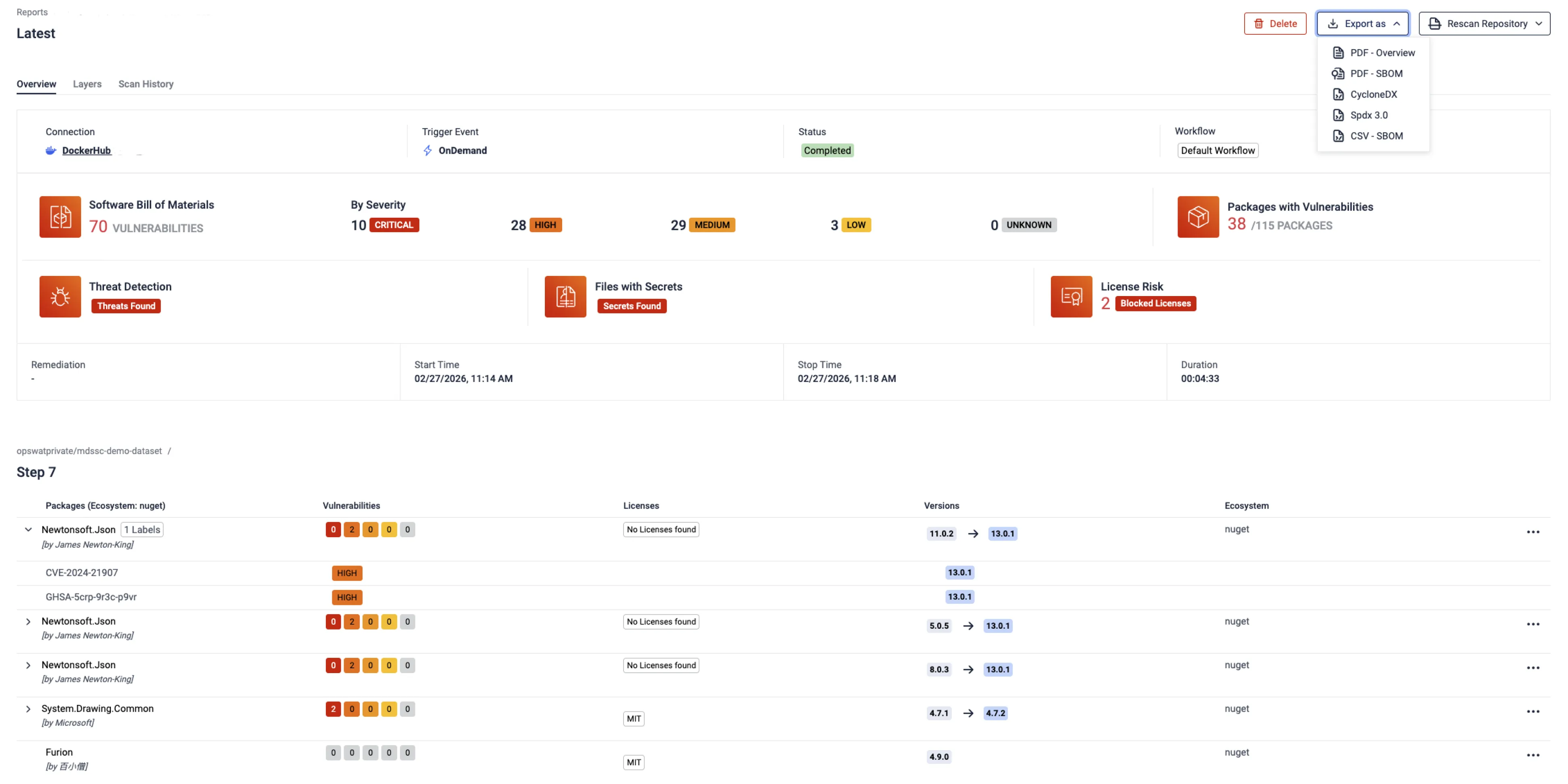
Shows the license type associated with each package alongside its detected version and available upgrade versions.
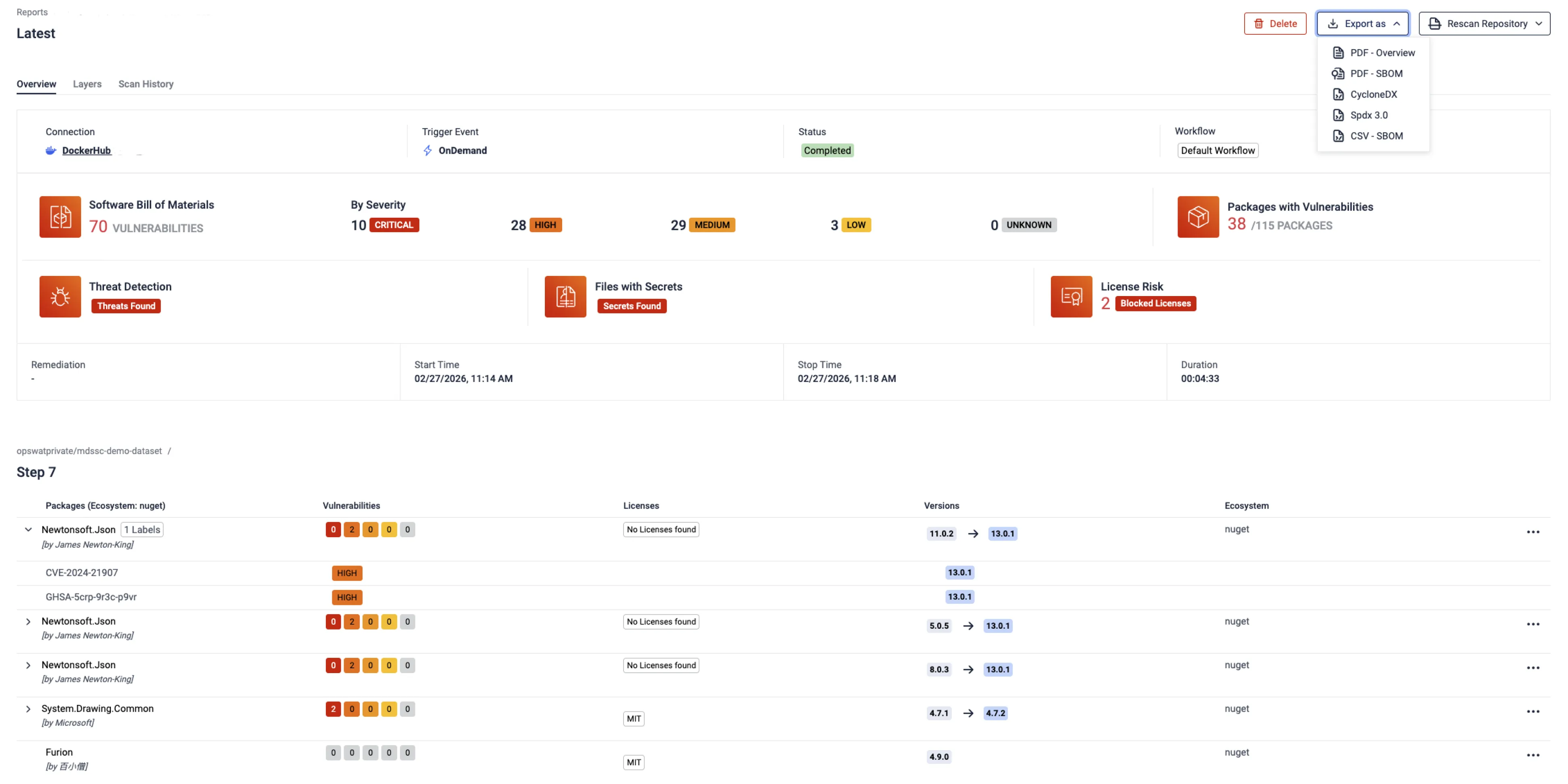
Highlights packages containing known vulnerabilities, with a detailed CVE breakdown by severity to help teams prioritize remediation.
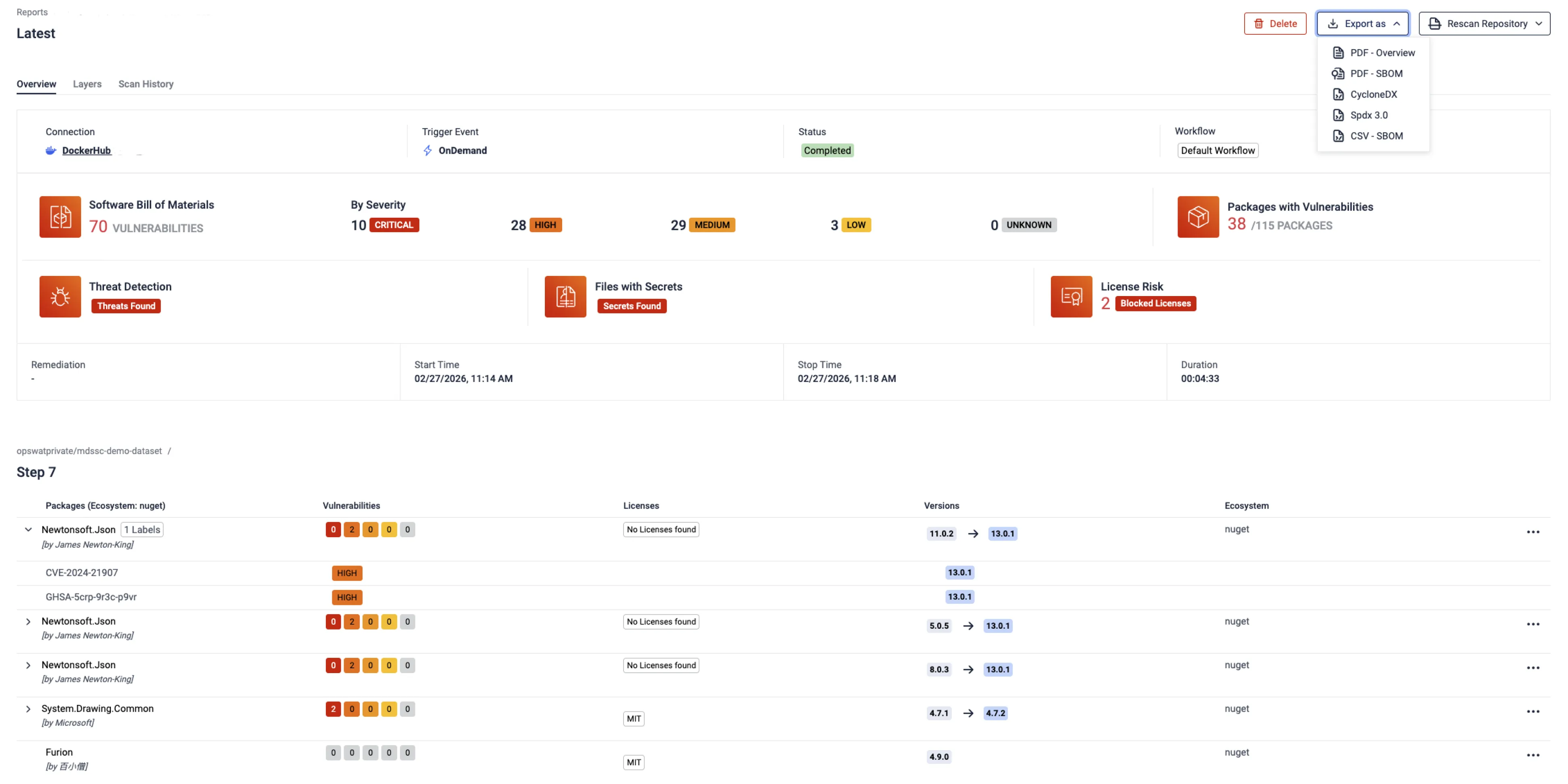
Allows export of scan results in multiple report and SBOM formats, including CycloneDX and SPDX.
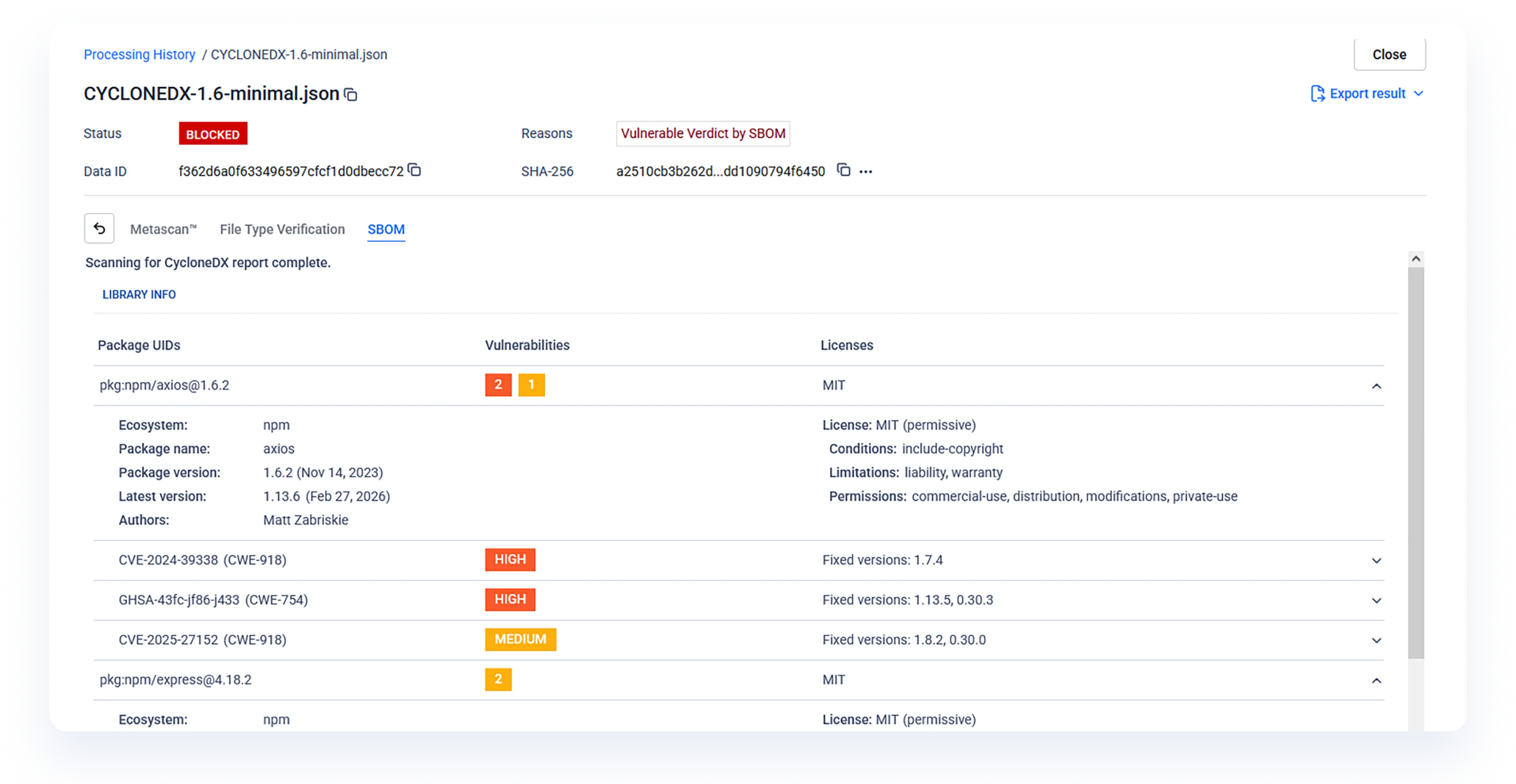
Import an existing SBOM report to verify its accuracy and automatically surface missing CVEs against up-to-date threat intelligence.
Upload any individual file for instant SBOM generation and vulnerability analysis — no repository integration required.
Integrations & Supported Languages
Cas d'utilisation
SBOM pour le code
Permettre aux développeurs d'identifier, de hiérarchiser et de traiter les vulnérabilités de sécurité et les problèmes de licence des dépendances open-source.

SBOM pour les conteneurs
Analyser les images de conteneurs et générer des SBOM pour le nom du paquet, les informations sur la version et les vulnérabilités potentielles.

SBOM pour la sécurité de Supply Chain
Secure la chaîne d'approvisionnement en logiciels à partir d'une plateforme unique afin d'accroître la sécurité, de réduire les risques et de fournir des logiciels sûrs.